Connected devices continuously collect data about daily life, creating a detailed portrait of activity. This raises clear trade-offs between convenience and autonomy, with ownership, consent, data minimization, and security at the core. The scope of data varies by device, app, and settings, often beyond initial expectations. Transparency, permissions, and configuration influence risk, yet gaps remain. As expectations of privacy tighten, a careful evaluation of practices and controls becomes essential to navigate future choices.
How Connected Devices Reveal Personal Privacy Trade-offs
Connected devices inevitably collect and transmit data about user behavior, settings, and environment, creating a granular portrait of daily life.
This analysis highlights trade-offs between autonomy and surveillance, urging scrutiny of data ownership, consent mechanisms, and data security.
Device transparency clarifies expectations, while robust safeguards enable informed choice; freedom hinges on clear rights, verifiable privacy practices, and enforceable standards that limit intrusion without stifling innovation.
What Data Really Gets Collected by Everyday Gadgets
The scope of data collected by everyday gadgets extends beyond obvious metrics such as usage counts and input selections to encompass seemingly innocuous signals, including device status, location traces, sensor readings, and ancillary metadata. Data collection practices reveal how device telemetry aggregates context, enabling inferences.
Privacy trade offs arise, demanding data minimization while preserving functional value and user freedom to assess risk.
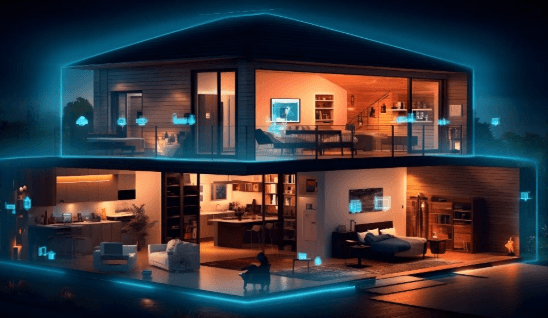
Practical Steps to Protect Your Privacy at Home
Practical steps to protect privacy at home involve a disciplined, methodical approach that prioritizes data minimization, secure configurations, and ongoing monitoring.
The analysis highlights privacy tradeoffs inherent in device choices and settings, urging deliberate configuration and routine audits.
Emphasis rests on limiting data collection, separating networks, and documenting policies, enabling informed, autonomous decisions while preserving functional freedom within a trustworthy home technology ecosystem.
Evaluating Privacy Features: Choosing Safer Devices and Apps
Selecting devices and apps with robust privacy features requires a disciplined evaluation of data collection practices, permission scopes, and default configurations.
Analysts emphasize privacy controls, data minimization, and transparent consent.
When assessing smart speakers and other tools, scrutiny of app permissions, data retention policies, and firmware updates helps preserve autonomy.
Precise choices reduce surveillance risks while preserving functional freedom.
See also: newsfault
Frequently Asked Questions
How Do I Exercise My Rights Over My Data With Manufacturers?
The question is answered: individuals may exercise privacy rights by requesting data access, deletion, and portability; enforce consent management preferences; and challenge vendors through regulatory bodies if needed, ensuring data portability, lawful processing, and transparent manufacturer practices.
Are Voice Assistants Always Listening After I Stop Speaking?
Are microphones always on, listening? No; typical devices await wake words, then record. Data collection transparency varies; consent notices and controls differ. The cautious analyst notes ongoing privacy risks, urging freedom-seeking users to review settings and minimize data sharing.
What Happens to My Data When I Delete an Account?
Deleting an account triggers privacy deletion and data retention checks; data may be removed, anonymized, or retained per policy and legal obligations, with timing varying. The process reflects caution, analytics, and a freedom-focused commitment to user control and transparency.
How Can I Verify Third-Party Apps’ Privacy Practices?
Third party apps should undergo privacy audits to verify practices, while consent management and data minimization concerns guide evaluation; this analytic approach enables users seeking freedom to assess privacy claims, ensuring robust transparency about third party apps.
Do Smart Devices Share Data With Advertisers by Default?
Yes, smart devices can share connected data with advertisers by default, though practices vary. The analysis emphasizes advertiser practices, privacy settings, and data sharing policies, urging users to scrutinize defaults and exercise control to preserve freedom.
Conclusion
In the quiet glow of smart devices, data threads weave a map of daily life, revealing patterns as delicate as footprints in frost. The balance between utility and exposure rests on careful choices: explicit consent, minimization, and segmented networks. When transparency is present and safeguards endure updates, households can inhabit a safer privacy landscape. Yet vigilance remains essential, for even a single unchecked permission can melt boundaries, turning intimate routines into accessible intelligence.